Login
This article needs additional citations for verification. (February 2024) |
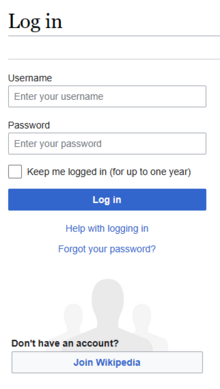
In computer security, logging in (or logging on, signing in, or signing on) is the process by which an individual gains access to a computer system or program by identifying and authenticating themselves.
The user credentials are typically some form of a username and a password,[1] and these credentials themselves are sometimes referred to as a login.[2]
In practice, modern secure systems often require a second factor such as email or SMS confirmation for extra security.
Social login allows a user to use an existing cell phone number, or user credentials from another email or social networking service to sign in or create an account on a new website.
When access is no longer needed, the user can log out, log off, sign out or sign off.
Procedure

Logging in is usually used to enter a specific page, website or application, which trespassers cannot see.
Once the user is logged in, the login token may be used to track what actions the user has taken while connected to the site.
Logging out may be performed when the user takes an action, such as entering an appropriate command or clicking on an external link. It can also be done implicitly, such as by the user powering off their workstation, closing a web browser window, leaving a website, or not refreshing a website within a defined period.
A login page may have a return URL parameter, which specifies where to redirect back after logging in or out. For example, it is returnto= on this site.
In the case of websites that use cookies to track sessions, when the user logs out, session-only cookies from that site will usually be deleted from the user's computer. In addition, the server invalidates any associations with the session, thereby making any session-handle in the user's cookie store useless.
This feature comes in handy if the user is using a public computer or a computer that is using a public wireless connection. As a security precaution, one should not rely on implicit means of logging out of a system, especially not on a public computer; instead, one should explicitly log out and wait for the confirmation that this request has taken place.
Logging out of a computer, when leaving it, is a common security practice preventing unauthorized users from tampering with it. There are also people who choose to have a password-protected screensaver set to activate after some period of inactivity, thereby requiring the user to re-enter their login credentials to unlock the screensaver and gain access to the system.
There can be different methods of logging in that may be via image, fingerprints, eye scan, password (oral or textual input), etc.
History and etymology

The terms became common with the time sharing systems of the 1960s and Bulletin Board Systems (BBS) in the 1970s.
Early home computers and personal computers did not generally require them until Windows NT, OS/2 and Linux in the 1990s.
The term login comes from the verb (to) log in and by analogy with the verb to clock in.
Computer systems keep a log of users' access to the system. The term "log" comes from the chip log which was historically used to record distance traveled at sea and was recorded in a ship's log or logbook.
To sign in connotes the same idea but is based on the analogy of manually signing a log book or visitor's book.
While there is no agreed difference in meaning between the terms login, logon and sign-in, different technical communities tend to prefer one over another – Unix, Novell, Linux and Apple typically use login, and Apple's style guide says "Users log in to a file server (not log on to)...".[3]
By contrast, Microsoft's style guides traditionally suggested the opposite and prescribed log on and logon.
In the past, Microsoft reserved sign-in to access the Internet,[4] but from Windows 8 onward it has moved to the sign-in terminology for local authentication.[5]
See also
- Computer security
- Credential lag
- Login session
- Login spoofing
- OpenID
- Password
- Password policy
- Personal identification number
- /var/log/wtmp
References
- ^ "Detail and definition of login and logging in". The Linux Information Project. Archived from the original on 25 December 2019. Retrieved 1 January 2014.
- ^ "Definition of login". Oxford Dictionaries. Archived from the original on 7 February 2014. Retrieved 8 February 2014..
- ^ "Apple Style Guide" (PDF). Apple. 30 April 2013. p. 96 & 97. Archived from the original (PDF) on 17 February 2015. Retrieved 17 May 2015.
- ^ "Use log on or log on to... Do not use log in, login", 2004, Manual of Style for Technical Publications, 3rd edition, p. 295, Microsoft.com.
- ^ "Sign in to or out of Windows". Microsoft. Archived from the original on 28 October 2012. Retrieved 28 October 2012.
